For the following business rules, a sample ERD is provided below. • A painter can paint may paintings. • Each painting is painted by only one painter. A gallery can exhibit many paintings. A painter can exhibit paintings at more than one gallery at a time. • Each painting is exhibited in only one gallery. A relationship between two entities in the ERD below has a participation symbol mistaken in one side. Click on the corresponding relationship line in the ERD below. PAINTER PAINTING PK Painter Num PK Painting Num Painter_LName paints Painting_Title но- Painter_FName FK Gallery Number Painter_Initial is shown in GALLERY PK Gal Num Gal_Name Gal_Web
For the following business rules, a sample ERD is provided below. • A painter can paint may paintings. • Each painting is painted by only one painter. A gallery can exhibit many paintings. A painter can exhibit paintings at more than one gallery at a time. • Each painting is exhibited in only one gallery. A relationship between two entities in the ERD below has a participation symbol mistaken in one side. Click on the corresponding relationship line in the ERD below. PAINTER PAINTING PK Painter Num PK Painting Num Painter_LName paints Painting_Title но- Painter_FName FK Gallery Number Painter_Initial is shown in GALLERY PK Gal Num Gal_Name Gal_Web
Related questions
Question
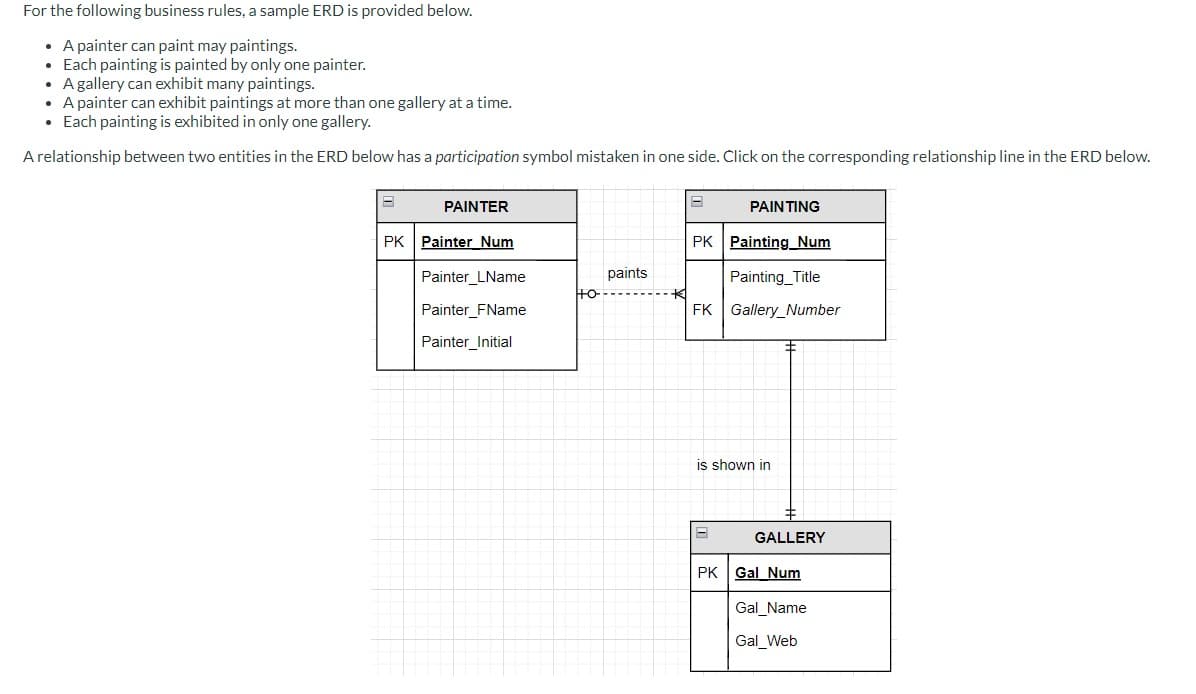
Transcribed Image Text:For the following business rules, a sample ERD is provided below.
• A painter can paint may paintings.
• Each painting is painted by only one painter.
A gallery can exhibit many paintings.
A painter can exhibit paintings at more than one gallery at a time.
• Each painting is exhibited in only one gallery.
A relationship between two entities in the ERD below has a participation symbol mistaken in one side. Click on the corresponding relationship line in the ERD below.
PAINTER
PAINTING
PK Painter Num
PK Painting Num
Painter_LName
paints
Painting_Title
но-
Painter_FName
FK Gallery Number
Painter_Initial
is shown in
GALLERY
PK Gal Num
Gal_Name
Gal_Web
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 2 steps
